This week on The Awareness Angle, 70,000 government ID images are exposed in a Discord age verification breach, staff data is hit at the European Commission, and supplier fallout ripples out to Volvo Group after a third party incident. More data. More dependency. More risk.
We also cover Apple’s emergency zero day patch already being exploited in the wild, a devastating AI deepfake investment scam that cost an 82 year old nearly £200,000, and fresh concerns around autonomous AI agents expanding enterprise attack surfaces faster than governance can keep up.
On top of that, we get into the backlash around Ring’s Super Bowl advert and surveillance partnerships, why some organisations are banning Notepad++ instead of simply patching it, and how email bombing is still being used to quietly bury real account compromise in a flood of noise.
All of that, and a few strong opinions along the way, in this week’s edition of The Awareness Angle.
The Awareness Angle is best served in full. Watch on YouTube, listen on Spotify, Apple Podcasts, or wherever you get your podcasts. If you like your cyber news with context, challenge, and the occasional raised eyebrow, this one’s for you.
Watch or listen to the episode today - YouTube | Spotify | Apple Podcasts
Visit riskycreative.com for past episodes, our blog, and our merch.
This Week's Stories...
Discord Faces Backlash After Age Verification Breach
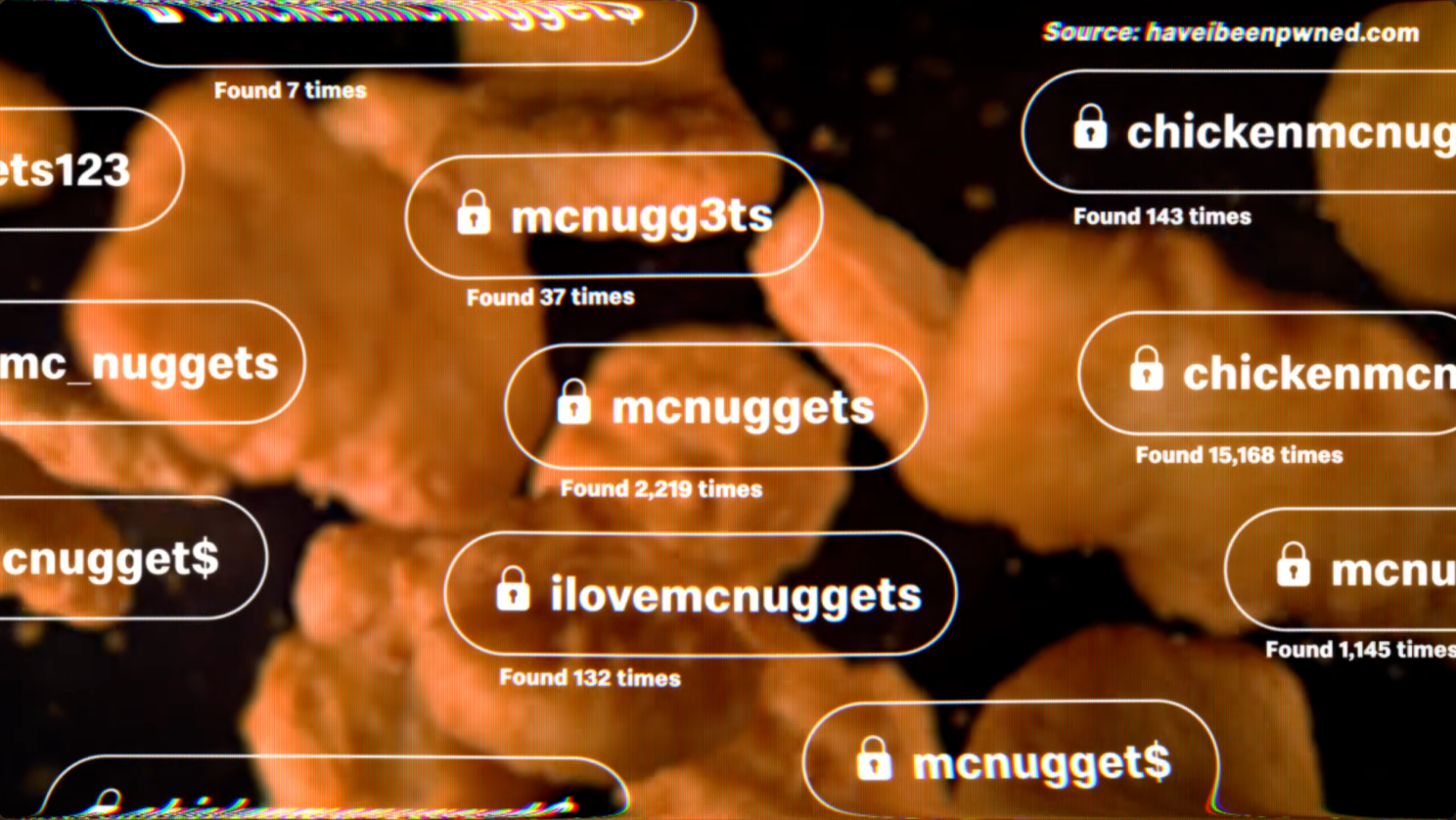
Around 70,000 government issued ID images were exposed after a third party provider used for age verification was compromised. These were not usernames. Not email addresses. Actual passport and driving licence images.
This is where the age verification debate gets uncomfortable.
We said on the podcast that this is the trade off problem in real time. If platforms require more sensitive data to prove age, the impact of failure increases massively. And crucially, it is not just about trusting the platform. It is about trusting who they trust.
This was not Discord’s core infrastructure being breached. It was a supplier in the chain. But to the user whose passport is now exposed, that distinction does not matter.
Searches for Discord alternatives reportedly spiked after the story broke. That is what trust erosion looks like.
The Awareness Angle
- More Data, More Risk – The more sensitive the data collected, the higher the impact if breached.
- Third Parties Matter – Your risk extends to every supplier in the chain.
- Trust Has a Cost – Safety controls must not create bigger privacy problems.European Commission Discloses Staff Data Breach
European Commission Discloses Staff Data Breach
The European Commission confirmed a breach affecting a system used to manage staff mobile devices. Personal data such as names and contact details may have been accessed. There is currently no indication that classified systems were compromised.
The bigger issue is what happens next.
Internal directories and HR data are high value targets. Once exposed, they fuel phishing, impersonation and social engineering.
Containment reportedly happened within hours. But the exposure still matters.
The Awareness Angle
- Staff Data Is High Value – Internal directories and HR data are prime targeting fuel.
- Breaches Enable Follow On Attacks – Exposure often leads to phishing and impersonation.
- Compliance Is Not Immunity – Even major institutions remain attractive targets.
Volvo Group Impacted by Conduent Supplier Breach
Volvo Group has been named among organisations impacted by a cyberattack at IT services provider Conduent.
This is another reminder that your organisation’s risk surface is bigger than your own firewall.
Conduent provides back office services such as document processing and administrative support. When a service provider like that is breached, the impact cascades outward. One breach can affect dozens, sometimes hundreds, of downstream organisations.
We have said it before, but this is third party concentration risk in action. If one supplier services many large brands, the blast radius expands dramatically.
Volvo is not alone here. And that is the point.
The Awareness Angle
- Third Party Risk Is Shared Risk – Your exposure includes your suppliers.
- One Breach, Many Victims – Service providers create amplified blast radius.
- Supply Chain Visibility Matters – Know who holds your data, and how it is protected.
Apple Fixes Actively Exploited Zero Day
Apple released emergency updates to patch a zero day vulnerability described as being used in “extremely sophisticated” attacks.
When a vendor confirms exploitation is already happening, patching becomes urgent.
These flaws are rarely theoretical. They are used in targeted campaigns. Targeted does not mean rare. It means deliberate.
The Awareness Angle
- Zero Days Are Real World – These are not theoretical flaws. They are exploited.
- Targeted Does Not Mean Safe – Sophisticated attacks still affect everyday users.
- Update Culture Matters – Fast patching is still one of the strongest defences.
82 Year Old Loses £200k in AI Deepfake Investment Scam
An 82 year old grandmother lost nearly £200,000 after seeing what appeared to be a trusted doctor promoting an investment opportunity in a professional looking video.
It was AI generated.
The scam did not rely on broken English or obvious red flags. It relied on authority bias, emotional manipulation, and realism. Conversations continued over Messenger. Funds were moved into cryptocurrency. The emotional driver was securing care for her autistic grandson.
We said this on the show. This is not clumsy phishing. This is AI realism combined with psychology.
One comment we discussed summed it up well. It is easy to look at stories like this and think gullible old people. But the speed at which AI is improving should make all of us pause. The bar for deception is rising quickly.
The Awareness Angle
- Trust Can Be Faked – Familiar faces are no longer proof.
- Crypto Is Hard to Reverse – Once funds move, recovery is unlikely.
- Emotion Drives Decisions – Scammers exploit care, not just greed.
This Week's Discussion Points...
🔎 Breach Watch
Discord Age Verification Breach Exposes 70,000 Government IDs Watch | Read
European Commission Discloses Staff Data Breach Watch | Read
Volvo Group Impacted by Conduent Data Breach Watch | Read
Apple Fixes Zero Day Used in Highly Sophisticated Attacks Watch | Read
Our Org Is Banning Notepad++ After Supply Chain Concerns Watch | Read
📰 News
82 Year Old Loses £200k in AI Deepfake Doctor Investment Scam Watch | Read
Reddit discussion: Read
Amazon Distances Itself From Flock Safety After Ring Super Bowl Backlash Watch | Read
How to Recognise a Deepfake, and Why It Is Getting Harder Watch | Read
OpenClaw Integrates VirusTotal After Enterprise Risk Warnings Watch | Read
💬 Discussion & Extras
Cloudflare “ClickFix” Style Fake Verification Page Watch | Read
Email Bomb Used to Hide a Real Security Alert Watch | Read
The CivDiv No.1 TikTok Account Recommendation Watch | TikTok
Most Common 4 Digit PIN Numbers Visualised Watch
QR Code Binder for Child Safe YouTube Access Watch
And finally...LinkedIn AI Caricature Trend Raises Oversharing Questions
See content credentials
A new trend circulating on LinkedIn has people using AI to generate caricature style action figure versions of themselves. These posts often include job titles, hobbies, favourite sports teams, pets, cities, personality traits and sometimes even family details.
The trend itself feels creative and harmless. But a post this week from Matthew Jary highlighted something worth pausing on. When you scroll through a feed full of these, you start learning a surprising amount about complete strangers.
Individually, each detail seems insignificant. Collectively, they form a profile.
Many of the attributes being shared mirror the kinds of prompts commonly used in password reset questions and social engineering attempts. First pet. Favourite team. Hometown. Employer.
But here’s the alternative view.
Is this actually an issue?
Most of us openly share our job titles, employers, locations and interests on LinkedIn every day. That is the whole point of the platform. So is this genuinely risky, or is this just the latest “security people hate fun” moment? Is this simply anti bandwagon commentary?
Maybe.
The difference might not be the individual data point. It might be the packaging. When everything is neatly summarised in one visual snapshot, it lowers the effort required to profile someone.
This is not about banning fun. It is about understanding aggregation. Attackers do not always need a breach when information is voluntarily shared and easily searchable.
The risk is rarely one post. It is the accumulation.
The Awareness Angle
- Small Data Adds Up – Individual facts feel harmless. Combined, they become profile building fuel.
- OSINT Is Powerful – Attackers do not need a database leak if the information is public.
- Aggregation Changes Context – One detail is normal. A curated snapshot lowers the barrier for profiling.
Thanks for reading! If you’ve spotted something interesting in the world of cyber this week, a breach, a tool, or just something a bit weird, let us know at hello@riskycreative.com. We’re always learning, and your input helps shape future episodes.
Ant Davis and Luke Pettigrew write this newsletter and podcast.
The Awareness Angle Podcast and Newsletter is a Risky Creative production.
All views and opinions are our own and do not reflect those of our employers.