Supply Chain Hacks. Fake Encryption. Phones That Track You

This week on The Awareness Angle, a developer tool update chain gets quietly hijacked, ransomware actors claim access to airport systems, and law enforcement moves in on a major hacking forum, with questions over how much impact that will really have.
We also look at how phones can be tracked at the network level without apps or permission, why McDonald’s felt the need to call out terrible password habits, and how a chaotic extortion group is turning data breaches into deeply personal harassment campaigns. On top of that, Spain is moving to ban social media for under 16s, and questions are resurfacing about whether end to end encryption really means what people think it does.
All of that, and more, in this week’s edition of The Awareness Angle.
The Awareness Angle is best served in full. Watch on YouTube, or listen on Spotify or your favourite podcast platform to get the complete discussion and context.
🎧 Listen on your favourite podcast platform - Spotify, Apple Podcasts and YouTube

Listen Now
Podcast · Risky CreativeThis week's stories...
Notepad++ update chain compromised
Notepad++, a tool a lot of developers use without a second thought, was caught up in a supply chain attack that didn’t touch the code at all. Instead, attackers went after the update process. Between June and December 2025, a small number of users were redirected to malicious update files through the hosting infrastructure.
This wasn’t random. It looks deliberate and targeted, likely aimed at developers or organisations working on sensitive projects. The software itself was fine, but the trust people place in automatic updates was the weak point. Notepad++ has since moved hosting providers, tightened up how updates are verified, and confirmed that versions 8.8.9 and above are safe.
It’s one of those stories that feels uncomfortable because it hits a blind spot. We trust tools like this precisely because they are familiar and boring.
The Awareness Angle
- The risk lived outside the app - The problem wasn’t what people installed, it was what they never see, the update mechanism.
- Targeted still counts - You don’t need to hit everyone, just the right few people.
- Choice brings exposure - Every extra tool adds convenience and risk, which is why organisations try to limit what gets installed.
Ransomware group claims access to airport systems
A ransomware group is claiming it breached systems linked to Tulsa International Airport and has begun dumping internal files online as proof. The attackers say the data includes internal emails, employee IDs, passports, and financial documents. At the time of reporting, the airport has not publicly confirmed the breach and the leaked material has not been independently verified.
That uncertainty is part of the tactic. Modern ransomware groups do not just rely on encryption or extortion notes. They use public claims and data leaks to create pressure, force attention, and shape the narrative before facts are fully known. Airports are particularly exposed to this kind of pressure because disruption, even perceived disruption, carries immediate reputational and operational weight.
Verified or not, once claims and files are public, the human impact starts straight away.
The Awareness Angle
- Pressure starts before proof - Publishing claims and documents is designed to trigger panic and rushed decisions.
- Visibility increases impact - Highly visible organisations feel the reputational damage faster, even when details are unclear.
- Pause is a defence - Calm, verification, and controlled communication matter more than speed in moments like this.
Your phone can be tracked without your permission, and most people do not realise it
Most people think they understand how location tracking works. If an app does not have permission, or GPS is turned off, they assume their phone is no longer sharing where they are. This story shows that is not how it actually works.
Mobile networks can locate phones at the carrier level using systems originally built for emergency services. This sits below iOS and Android, which means your phone never asks you, and you never see it happening. It is not malware and it is not a bug. It is how mobile infrastructure has worked for years.
When we talked about this on the podcast, the bit that really landed was how normal this feels once you realise it has been there the whole time. The technology did not change. Our assumptions did.
The Awareness Angle
- Permissions feel reassuring - Turning things off gives a sense of control, even when it does not change the outcome.
- The real risk is invisible - Tracking can happen below apps and operating systems people interact with.
- Assumptions shape behaviour - When beliefs are wrong, people take risks without realising it.
This Week's Discussion Points...
Notepad++ supply chain attack Watch | Read
Ransomware group claims access to airport systems Watch | Read
FBI seizes RAMP hacking forum Watch | Read
Lawsuit claims WhatsApp encryption is a lie Watch | Read
Spain announces social media ban for under 16s Watch | Read
Your phone can be tracked without your permission Watch | Read
Scattered Lapsus ShinyHunters extortion tactics Watch | Read
Ransomware attacks up 30 percent Watch | Read
Ant's mum targeted by follow up scam call Watch
McDonald’s calling out weak passwords Watch | Read
Getting your first job in cybersecurity Watch | Read
Real or phishing, shockingly bad campaign emails Watch | Read
And finally...McDonald’s calling out weak passwords, and it lands because it’s honest
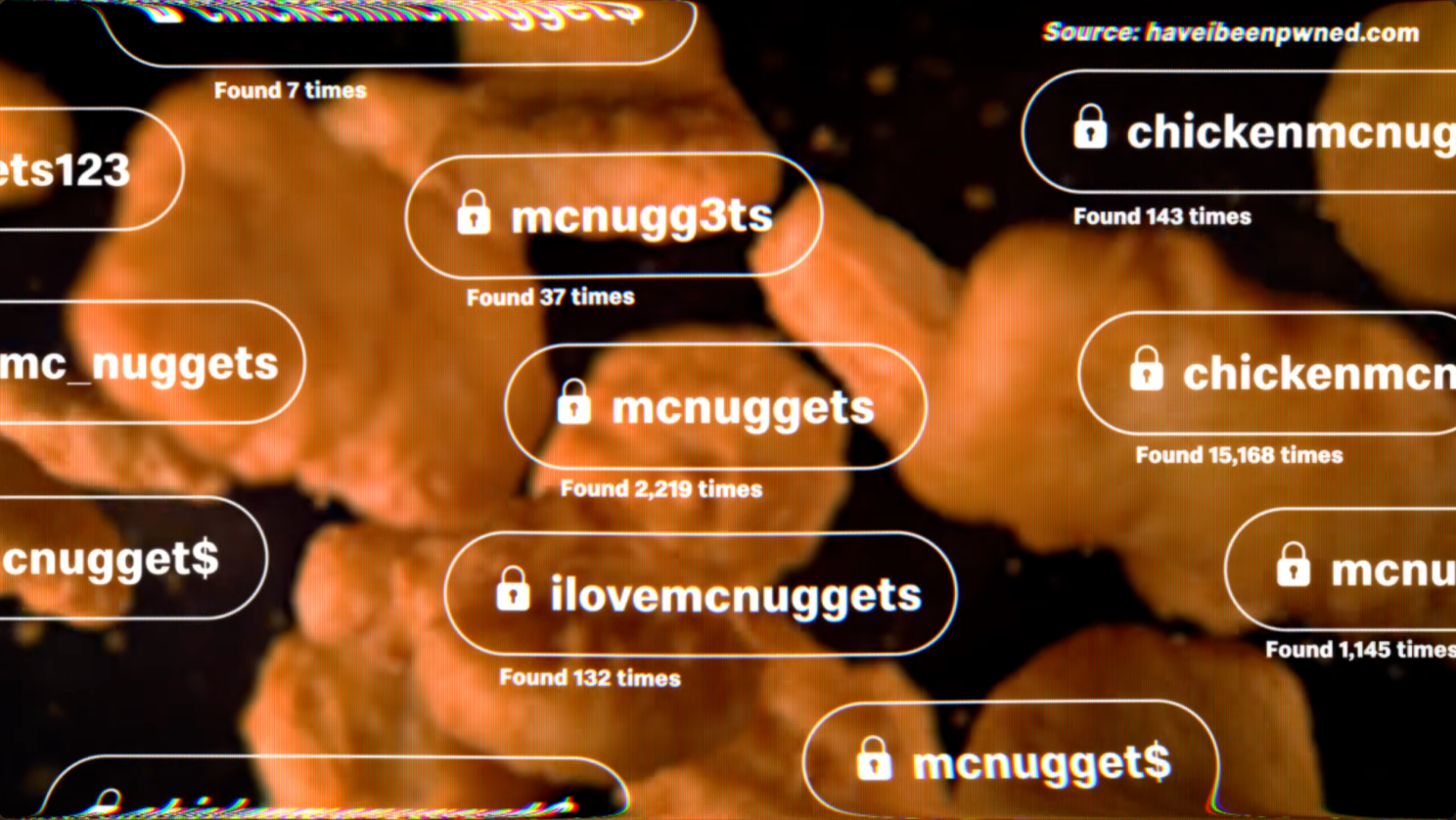
McDonald’s Netherlands used Change Your Password Day to highlight something security teams have been saying for years. People choose passwords based on things they like, recognise, or can remember. BigMac, HappyMeal, McNuggets, and endless variations of them showed up tens of thousands of times in breached password data.
As we said on the show, this works because it doesn’t pretend people are suddenly going to behave like security professionals. It accepts reality and designs around it.
Predictability is the real problem. Swapping letters for numbers or adding a symbol feels clever, but attackers expect it. Tools try those combinations automatically. The habit hasn’t changed, even though the threat has.
What’s interesting is how transferable this idea is. Almost any organisation could do a version of this with their own language, products, acronyms, or in jokes. When people see themselves reflected in the message, it lands very differently.
The Awareness Angle
- Familiar beats secure - People choose passwords that feel personal and memorable, not resilient.
- Old advice lingers - Leetspeak and small tweaks still feel protective, even though they stopped working years ago.
- Make it local - Campaigns are more effective when people recognise their own habits and language in the message.
Would you try this in your organisation? Let us know by getting in touch at hello@riskycreative.com